Executive Summary
Most API versioning failures are not technical failures they are contract failures. Engineering teams ship breaking changes without realizing it, deprecate endpoints without warning, or lock themselves into a versioning scheme that collapses under the weight of a growing product. This article covers how my team designs versioning systems that survive years of product evolution without breaking integrations.
The Real Problem This Solves
Every API is a public contract. The moment a client internal service, third-party integration, mobile app, enterprise customer starts consuming your API, you have made an implicit promise: this will keep working.
The problem is that products change. Business logic evolves. Data models get restructured. Authentication schemes get upgraded. And at some point, the API you designed eighteen months ago no longer maps cleanly to the system you are running today.
Without a deliberate versioning strategy, you face a brutal choice: break existing integrations to move forward, or freeze your API in amber and carry the technical debt forever. Neither is acceptable.
The real damage shows up in enterprise sales cycles. A potential customer’s integration team asks: “What is your deprecation policy?” If your answer is vague, the deal slows down. If your answer is “we’ve broken clients before,” the deal dies. API stability is directly tied to revenue trust at scale.
The Four Versioning Models and What They Actually Cost You
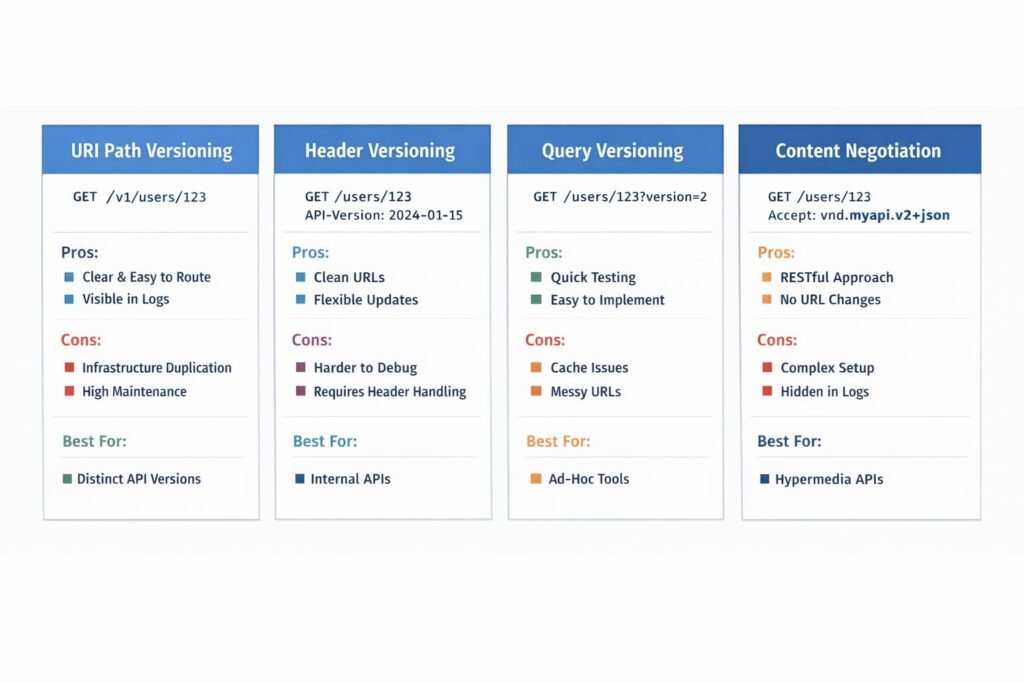
URI Path Versioning
This is the most common approach and the easiest to reason about:
GET /v1/users/123
GET /v2/users/123
The version lives in the URL. Routing is explicit. Clients know exactly what they are hitting. Caches work correctly. Logs are easy to filter.
The cost is infrastructure multiplication. Every major version is essentially a parallel API surface. My team has run systems where /v1, /v2, and /v3 all lived simultaneously three separate route trees, three sets of validation logic, three deprecation timelines to manage. At that point, versioning becomes a maintenance burden that competes with feature development.
URI versioning works well when your major versions are genuinely distinct product surfaces not just incremental changes. If you are shipping a /v2 because you added two new fields to a response object, you are using a sledgehammer where a scalpel was needed.
Header-Based Versioning
The version travels in a request header rather than the URL:
GET /users/123
API-Version: 2024-01-15
This keeps URLs clean and semantically stable. The resource identity /users/123 does not change between versions. Only the representation changes.
Stripe and GitHub use date-based header versioning. My team has adopted this for internal platform APIs where URL cleanliness matters and clients are sophisticated enough to manage headers deliberately.
The downside is debuggability. When a client reports a bug, the first question is always “which version are you on?” With URI versioning, that is visible in logs immediately. With header versioning, you need to ensure your logging pipeline captures and indexes the version header which sounds trivial until you are tracing an incident at 2 AM across five microservices.
Query Parameter Versioning
GET /users/123?version=2
My team treats this as a last resort. It works, but it pollutes query semantics, breaks cache key design, and is easy to strip accidentally by intermediary proxies. The only place this makes sense is in exploratory or internal tooling APIs where clients are developers running ad-hoc queries.
Content Negotiation Versioning
GET /users/123
Accept: application/vnd.myapi.v2+json
This is the most RESTfully pure approach and the least practical one. It requires clients to set non-standard Accept headers, breaks most API testing tools out of the box, and makes the versioning invisible in standard HTTP logs. My team has never shipped this in production and would not recommend it for anything other than a hypermedia API with a deeply invested client base.
The Architecture That Actually Scales
The versioning model you choose is less important than the internal architecture that supports it. Here is how my team structures versioning to minimize long-term pain.
The Transformation Layer Pattern
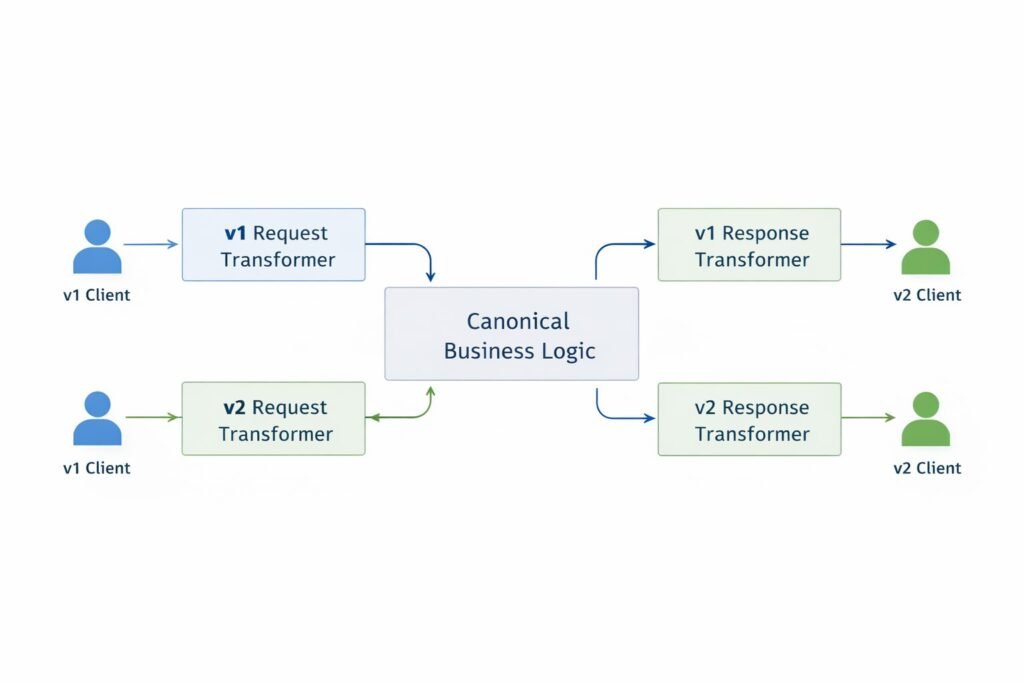
Rather than maintaining parallel codebases for each API version, my team runs a single internal business logic layer and a version-specific transformation layer at the boundary.
The flow looks like this: an incoming v1 request hits a v1 request transformer that normalizes it to the internal canonical format. Business logic executes against the canonical format. The response passes through a v1 response transformer before being returned to the client.
When v2 ships, you add a v2 transformer pair. The business logic layer does not change. You are only managing input/output shape differences at the edge, not forking your entire service.
This architecture means a bug fix in the business logic layer automatically benefits all API versions simultaneously. You are not backporting fixes across parallel codebases.
The transformation layer works best when version differences are representational field renames, response structure changes, added or removed properties. It breaks down when versions have fundamentally different behavioral contracts, in which case you genuinely do need parallel logic.
Versioning Granularity: API-Level vs. Resource-Level
Most teams version at the API level: /v2/ bumps the entire API surface. My team has found that resource-level versioning is significantly more maintainable at scale.
With resource-level versioning, only the resources that actually changed get a new version. /v1/users stays at v1. /v2/payments exists because the payments resource changed. /v1/products stays at v1 because nothing changed there.
The routing logic becomes slightly more complex, but the deprecation burden drops dramatically. You are not forcing clients to migrate the entire API integration when only one resource changed.
The Deprecation Protocol
Versioning without a deprecation protocol is half a strategy. Here is what my team enforces in production:
Step 1 Announce deprecation via response headers. When a client hits a deprecated endpoint, the response includes:
Deprecation: true
Sunset: Sat, 01 Mar 2026 00:00:00 GMT
Link: <https://api.example.com/v2/users>; rel=”successor-version”
This gives clients programmatic visibility into deprecation without requiring them to read documentation.
Step 2 Active client notification. My team queries API logs to identify every client still hitting deprecated endpoints thirty days before sunset. We reach out directly email, in-app notification, account manager escalation for enterprise clients. Passive deprecation announcements in changelogs are not sufficient.
Step 3 Traffic monitoring through the sunset window. Even after the announced sunset date, my team monitors for residual traffic before actually removing the endpoint. Real-world integrations are maintained by teams with their own sprint cycles, and a hard cutoff on the exact sunset date creates incidents for clients who were mid-migration.
Step 4 Tombstone, do not delete. After sunset, replace the endpoint with a 410 Gone response that includes the migration URL in the body. Do not return a 404. A 410 communicates “this was here and is now intentionally removed,” which is materially different from “this never existed.” It gives engineers a path forward instead of a wall.
Engineering Decisions and Real Trade-offs
Breaking vs. Non-Breaking Changes
My team maintains an explicit classification system for every API change:
Non-breaking (safe to ship without a version bump):
- Adding new optional fields to a response
- Adding new optional request parameters
- Adding new endpoints
- Expanding enum values (with caution clients that switch on enum values exhaustively will break)
- Relaxing validation rules
Breaking (requires a version bump or careful migration):
- Removing fields from a response
- Renaming fields
- Changing field types (string to integer, object to array)
- Changing authentication schemes
- Tightening validation rules
- Changing HTTP status codes for existing conditions
- Modifying pagination behavior
The category that trips up most teams is behavioral breaking changes changes where the fields stay the same but the semantics change. Changing when a status field transitions from pending to active, for example, is a breaking change even if the field name and type are identical. My team documents behavioral contracts explicitly and treats behavioral changes with the same discipline as structural ones.
Versioning and API Gateways
If you are running an API gateway Kong, AWS API Gateway, Nginx-based routing the gateway is the natural home for version routing logic. Route /v1/* to service cluster A, /v2/* to service cluster B, or use the gateway to inject version headers before forwarding to a unified backend.
The gateway approach gives you traffic splitting for gradual migration: route 5% of v2 traffic to the new implementation while 95% still hits the old path. This is how my team validates v2 behavior in production without committing to a full cutover.
Security Implications
API versioning introduces security surface area that most teams underestimate.
Old versions carry old vulnerabilities. If you shipped a security fix in v2, you must backport it to v1 for as long as v1 is live. My team maintains an explicit security backport policy: all security patches apply to all active versions, regardless of planned deprecation timeline. A version scheduled for sunset in three months is still live today and still needs to be patched.
Authentication scheme transitions are high-risk. Moving from API keys to OAuth 2.0 between versions a common migration means running two authentication systems simultaneously during the transition window. Each system needs to be hardened independently. My team treats the transition window as an elevated security risk period with additional monitoring.
Version header spoofing. With header-based versioning, a client can claim to be on any version. Ensure your authorization logic does not vary by version in ways that could be exploited do not grant different permission scopes to different versions of the same endpoint. If you are building on OAuth 2.0 in REST APIs, your token validation must be version-agnostic.
Zombie endpoints. The most common API security failure my team audits is endpoints that were “removed” from documentation but not from the router. Audit your route tables against your documentation regularly. Undocumented endpoints are not secure endpoints they are just unmonitored ones.
Performance Bottlenecks
Transformation Layer Overhead
The transformation layer pattern adds serialization/deserialization overhead at the API boundary. For most APIs, this is negligible microseconds per request. For high-frequency, low-latency APIs processing tens of thousands of requests per second, it is measurable.
My team benchmarks transformation overhead during load testing and sets a budget: transformation must add no more than 2ms to p99 latency. If a transformation exceeds that budget, it gets optimized or the versioning approach for that endpoint gets reconsidered.
Version Routing Complexity
As the number of active versions grows, routing logic becomes a performance and maintainability concern. My team enforces a maximum of three simultaneously active major versions. Beyond three, the operational overhead security patching, regression testing, transformation maintenance exceeds the cost of forcing clients to migrate.
Common Mistakes My Team Has Seen
- Treating every change as a major version bump. This trains clients to ignore version updates because they happen constantly. Reserve major versions for genuinely breaking changes.
- No machine-readable deprecation signals. Deprecation notices in a changelog that no one reads are not a deprecation strategy. Use Deprecation and Sunset headers.
- Versioning the entire API when only one resource changed. Forces unnecessary migrations on clients who do not consume the changed resource.
- Deleting endpoints instead of tombstoning them. A 404 where a 410 should be wastes hours of debugging time for every affected client.
- Not testing old versions in CI. My team has caught v1 regressions introduced by shared library upgrades that were only caught because v1 test suites still ran in the pipeline.
- Assuming internal APIs do not need versioning. Internal APIs become external APIs faster than anyone anticipates. Design them with versioning from the start.
When Not to Use This Approach
Formal API versioning with transformation layers, deprecation headers, and multi-version routing is the right architecture for APIs with external consumers. It is overkill in several contexts:
Early-stage internal APIs where the only consumers are teams within the same organization and migration can be coordinated synchronously. At this stage, just communicate the change and update all consumers in the same release.
Event-driven systems where the “API” is a message schema rather than an HTTP endpoint. Schema versioning in Kafka or SQS follows different patterns Avro schema registries, envelope versioning than HTTP API versioning.
Single-client APIs purpose-built for one integration. If exactly one system consumes your API and you control both sides, the overhead of formal versioning is waste. Use a feature flag or a deployment coordination instead.
Rapid prototyping phases. Versioning infrastructure before product-market fit locks you into patterns you may need to abandon. Build it once the API surface has stabilized enough to be worth protecting.
Enterprise Considerations
Enterprise buyers evaluate your versioning strategy as a proxy for organizational maturity. A well-documented deprecation policy signals that you have shipped APIs before, that you understand the cost of breaking integrations, and that you take the integration burden on your customers seriously.
My team maintains a public API stability commitment that covers three things: minimum notice period before deprecation (90 days for minor versions, 12 months for major versions), the communication channels used (email, in-app, developer portal), and the support available during migration (dedicated migration guides, compatibility libraries where applicable).
For large enterprise clients with long procurement and integration cycles, my team negotiates extended support windows contractually. A client that completed a six-month integration project is not going to accept a 90-day deprecation window. Enterprise SLAs often include versioning commitments that outlast standard deprecation timelines factor this into your architecture decisions before you commit to a sunset date publicly.
Compliance implications: In regulated industries, API versioning records serve as audit artifacts. If a financial services client needs to demonstrate that their integration behaved consistently during a regulatory audit period, your version history and deprecation records are part of that evidence chain. Store versioning metadata durably.
Cost & Scalability Implications
Running multiple API versions simultaneously has real infrastructure costs that are easy to underestimate at the outset.
Compute: If each version runs in an isolated service, you are paying for parallel infrastructure. At low traffic volumes, this is negligible. At scale, running three versions of a high-traffic API triples the compute baseline for that service.
Testing: Each active version needs its own regression test suite. Three active versions means three times the test maintenance burden. My team amortizes this by testing the transformation layer independently from the business logic, so business logic tests run once and transformation tests run per-version.
On-call burden: Every active version is a potential incident surface. A degradation in v1 is still a production incident even if 95% of traffic is on v3. My team factors active version count into on-call rotation complexity and uses it as a forcing function to drive deprecation timelines.
The migration incentive problem: Clients stay on old versions because migration is work they have to do and stability is the value they receive. My team has found that the most effective migration incentive is not deprecation pressure it is features. New capabilities only available on v2 pull clients forward faster than any sunset deadline. Design your versioning roadmap so that newer versions are meaningfully better, not just differently structured.
Implementing This Correctly: A Strategic Perspective
API versioning is infrastructure for trust. Done well, it signals to every integration partner, enterprise buyer, and developer consuming your platform that you take backward compatibility seriously that building on your API is a safe long-term investment.
My team approaches versioning in three layers. The first is technical: transformation layers, version routing, deprecation headers, and tombstone responses. These are engineering decisions that belong in your API design standards document before the first external client goes live.
The second is operational: deprecation protocols, client notification workflows, sunset monitoring, and security backport policies. These are process decisions that need ownership someone on your team is responsible for the deprecation calendar and client outreach, not just the codebase.
The third is contractual: stability commitments in your developer documentation, SLA addendums for enterprise clients, and public API changelogs that are accurate and current. This layer is what converts a well-engineered versioning system into a competitive advantage.
APIs compound in value over time. Every integration built on your platform, every workflow your customers automate, every enterprise system connected to yours all of it runs on the assumption that your API keeps working. Versioning is how you honor that assumption while still moving forward. Treat it as a strategic asset, not an engineering afterthought.
Finly Insights Team is a group of software developers, cloud engineers, and technical writers with real hands-on experience in the tech industry. We specialize in cloud computing, cybersecurity, SaaS tools, AI automation, and API development. Every article we publish is thoroughly researched, written, and reviewed by people who have actually worked in these fields.